슬롯사이트에서 즐기는 게임은 무궁무진한 재미와 스릴을 안겨줍니다. 하지만 더욱 특별한 경험을 원한다면 쿠폰,이벤트, 프로모션, 보증을 활용해보세요. 이들은 단순히 게임을 하는 것 이상의 혜택을 제공합니다. 첫째, 쿠폰은 보너스나 할인 혜택을 누리는 데 큰 도움을 줍니다. 이를 통해 자신의 자본을 효율적으로 운용할 수 있으며 보다 많은 돈을 벌 수도 있습니다. 더불어 이벤트에...
Continue reading...Fact Check
카지노사이트: 쿠폰, 이벤트, 프로모션, 보증으로 더욱 특별한 경험을!
카지노사이트를 방문하면서 게임을 즐기는 것만으로도 즐거운 시간을 보낼 수 있지만, 더욱 특별한 경험을 원한다면 쿠폰, 이벤트, 프로모션, 그리고 보증을 활용해보세요. 이러한 혜택들은 단순히 게임을 즐기는 것 이상의 특별한 혜택을 제공해줍니다. 많은 카지노사이트들은 회원들에게 다양한 혜택을 제공하기 위해 쿠폰 서비스를 제공하고 있습니다. 이런 쿠폰을 활용하면 보너스 포인트나 현금 등을 받을 수...
Continue reading...우리카지노 실제 이용자를 위한 완벽 가이드
우리카지노는 한국에서 가장 인기 있는 온라인 카지노 중 하나로 손꼽힙니다. 그들은 다양한 게임 옵션과 뛰어난 서비스로 많은 이용자들에게 사랑을 받고 있습니다. 우리카지노의 게임 우리카지노는 다양한 게임을 제공하여 이용자들이 심심할 틈이 없도록 합니다. 블랙잭, 룰렛, 슬롯머신 우리카지노 등 다양한 게임을 즐길 수 있습니다. 또한 실시간 딜러와 함께 하는 게임도 있어 현실적인...
Continue reading...안전놀이터: 이박사 플랫폼을 통한 최고의 선택 가이드!
안전놀이터 – 신뢰할 수 있는 놀이터 선택의 기준 안전놀이터는 사용자들에게 신뢰와 안정성을 제공하는 온라인 놀이터를 의미합니다. 이러한 놀이터는 엄격한 검증 과정을 거쳐 사용자들에게 안전한 놀이 환경을 보장합니다. 이 박사 플랫폼은 다양한 안전놀이터들을 추천하며, 사용자들이 각자의 필요에 맞는 최적의 놀이터를 쉽게 찾을 수 있도록 돕습니다. 이 박사 플랫폼의 추천은 빅데이터 분석...
Continue reading...연체자대출 해결사, 이지론으로 금융 고민 끝!
연체자대출의 정의와 이지론의 역할 연체자대출은 금융상의 어려움을 겪는 이들을 위한 대출 상품입니다. 이러한 상황에서 이지론은 빛과 같은 존재입니다. 이지론은 다양한 연체자대출 옵션을 제공하며, 사용자의 상황에 맞춘 최적의 해결책을 제시합니다. 이 플랫폼은 개인의 재정 상태, 대출 금리, 한도 등을 면밀히 분석하여 가장 적합한 대출 상품을 추천합니다. 이를 통해 연체자들은 더 낮은...
Continue reading...파워볼 예측의 새로운 지평: 베픽 커뮤니티의 혁신적 접근법
파워볼 예측의 중요성과 베픽의 역할 파워볼 예측은 많은 이들에게 단순한 게임이 아닌, 전략과 분석의 영역으로 자리 잡았습니다. 이러한 변화 속에서 베픽 커뮤니티는 사용자들에게 정교한 통계 기반의 예측 도구를 제공함으로써, 파워볼 게임에 대한 깊이 있는 이해와 전략적 접근을 가능하게 합니다. 베픽은 사용자들이 과거의 데이터, 추세, 그리고 다양한 분석 기법을 활용하여 보다...
Continue reading...카지노친구가 선별한 최상의 토토사이트
토토사이트: 안전과 신뢰의 보증 토토사이트는 사용자들에게 안전한 베팅 환경을 제공하기 위해 끊임없이 노력하고 있습니다. 이러한 사이트들은 엄격한 보안 조치와 더불어 빅데이터 기반의 검증 시스템을 통해 사용자들에게 신뢰를 보장합니다. 카지노친구는 이런 토토사이트들 중에서도 최고의 서비스와 보안을 자랑하는 업체들을 엄선하여 추천합니다. 카지노친구: 최상의 토토사이트 추천 서비스 카지노친구는 사용자들에게 최상의 토토사이트 추천 서비스를...
Continue reading...메이저사이트 선정과 이용을 위한 가이드
메이저사이트 소개: 신뢰할 수 있는 토토친구의 선택 메이저사이트는 온라인 배팅의 세계에서 신뢰와 안정성을 대표하는 플랫폼입니다. 토토친구에서 엄선하여 추천하는 이 사이트들은 사용자 경험, 안전성, 그리고 다양한 이벤트 및 프로모션으로 평가됩니다. 사용자들은 메이저사이트를 통해 다양한 스포츠 및 게임에 배팅할 수 있으며, 뛰어난 사용자 인터페이스와 고객 지원 서비스를 경험할 수 있습니다. 또한, 이...
Continue reading...여성알바 찾기의 시작, 미수다 커뮤니티와 함께하는 취업 여정
미수다: 여성알바 정보의 보고 미수다 커뮤니티는 여성알바를 찾는 이들에게 필수적인 정보의 보고입니다. 이곳에서는 다양한 산업군과 지역별로 분류된 알바 정보를 제공하며, 사용자들은 자신의 필요와 상황에 맞는 일자리를 쉽게 찾을 수 있습니다. 미수다에서 제공하는 정보는 신뢰할 수 있으며, 사용자들은 여기서 얻은 정보를 바탕으로 보다 나은 취업 결정을 내릴 수 있습니다. 급여와 취업...
Continue reading...안전놀이터: 플레이의 새로운 기준
안전놀이터 소개 안전놀이터는 온라인 게임 및 베팅의 새로운 장을 열었습니다. 이곳은 사용자들에게 안전하고 신뢰할 수 있는 게임 환경을 제공하며, 다양한 게임과 베팅 기회를 선사합니다. 특히, 이박사 플랫폼을 통해 엄선된 추천 및 보증업체들이 소개되어 사용자들이 더욱 안심하고 즐길 수 있습니다. 이곳에서는 빅데이터 기반의 분석을 통해 각 업체의 신뢰도를 검증하고, 이용자들에게 가장...
Continue reading...스웨디시 마사지: 건강과 휴식의 완벽한 조화
스웨디시 마사지는 근육의 긴장을 완화하고 전반적인 웰빙을 증진시키는 데 탁월합니다. 이 글에서는 스웨디시 마사지의 정의와 효과, 그리고 이를 제공하는 업체들의 서비스 비교에 대해 알아봅니다. 스웨디시 마사지란 무엇인가? 스웨디시 마사지는 부드럽고 편안한 스트로크를 사용하여 신체의 긴장을 풀어주고 혈액 순환을 촉진하는 마사지 방법입니다. 이는 휴식과 회복을 위한 최적의 방법 중 하나로 간주됩니다....
Continue reading...호빠알바 탐구: 남성들을 위한 새로운 취업 길잡이
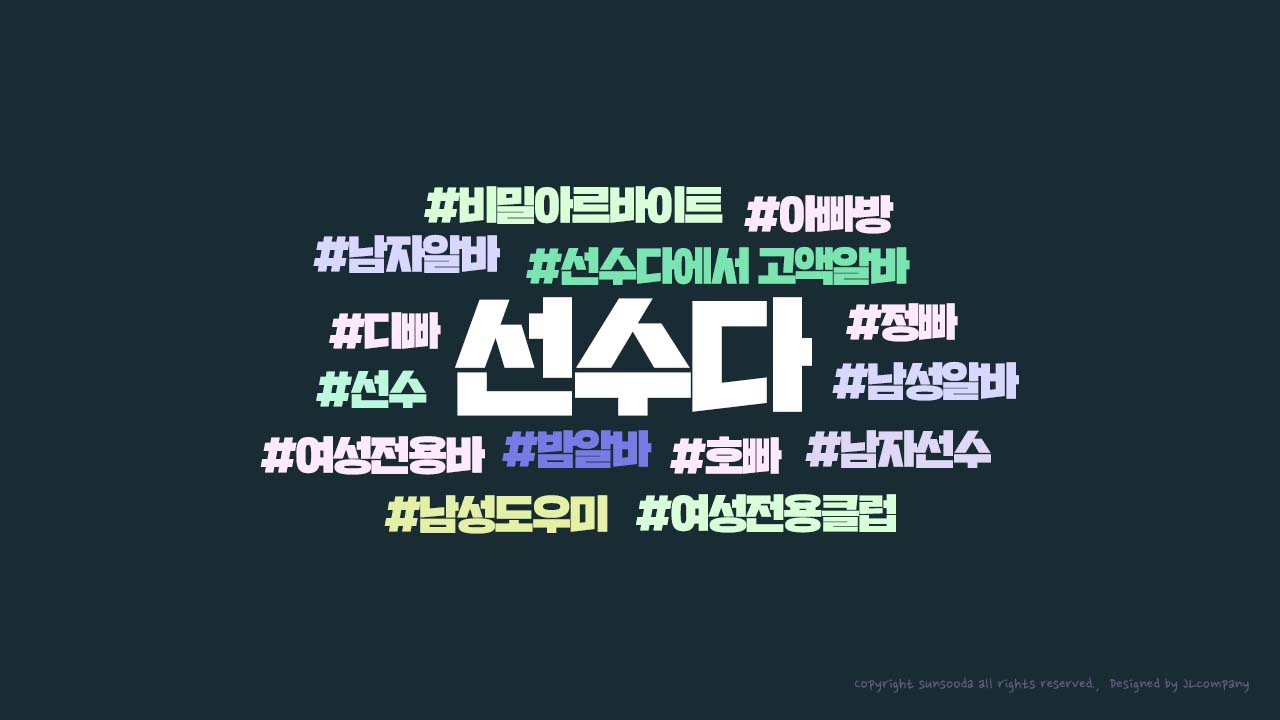
호빠알바, 즉 호스트바에서 일하는 남성 아르바이트에 대한 관심이 점차 증가하고 있습니다. 이 글에서는 호스트바 알바의 세계를 자세히 탐구해보겠습니다. 호스트바는 주로 여성 고객을 대상으로 서비스를 제공하는 업소입니다. 여기서 남성 직원들은 대화, 음료 서비스, 오락 등을 통해 고객에게 즐거운 시간을 제공합니다. 이 분야의 급여는 다양하며, 대부분의 호스트바는 시간당 또는 일당으로 지급합니다. 일부는...
Continue reading...카지노사이트의 세계: 최고의 추천과 순위
카지노사이트 추천의 기준 카지노사이트를 선택할 때 가장 중요한 요소는 신뢰성과 사용자 경험이다. 빅데이터 분석을 통해 사용자 선호도와 만족도가 높은 사이트들을 선별하여 추천한다. 이러한 사이트들은 보안, 고객 서비스, 게임의 다양성 및 공정성 면에서 우수하다는 평가를 받는다. 카지노사이트 순위의 중요성 카지노사이트 순위는 사용자들에게 유용한 정보를 제공한다. 순위는 게임의 품질, 보너스 및 프로모션,...
Continue reading...토토사이트의 세계: 빅데이터로 본 순위와 추천 업체들
사람들이 토토사이트를 선택할 때 가장 먼저 보는 것은 무엇일까요? 바로 ‘신뢰도’와 ‘사용자 리뷰’가 아닐까 합니다. 오늘은 토토친구가 제공하는 다양한 토토사이트 정보를 바탕으로, 여러분이 안전하고 즐겁게 베팅할 수 있는 공간을 찾는 데 도움을 드리고자 합니다. 토토사이트 순위의 비밀 토토사이트의 순위는 어떻게 매겨질까요? 빅데이터 분석은 이러한 순위를 정하는 데 중요한 역할을 합니다....
Continue reading...밤알바를 통한 새로운 기회의 발견
밤알바는 다양한 분야에서 새로운 기회를 찾는 사람들에게 매력적인 옵션입니다. 능동적인 직업 탐색에서부터 시작하여, 밤알바는 급여, 취업, 면접, 일자리 안내 등 다양한 측면에서 유용한 정보를 제공합니다. 이지알바는 밤알바에 대한 포괄적인 정보를 제공하는 플랫폼으로, 사용자들에게 업체목록, 업체소개, 지역별 및 업종별 업체정보 등을 제공합니다. 이를 통해 구직자들은 자신의 요구와 기대에 맞는 최적의 일자리를...
Continue reading...